Cloud can be tricky sometimes. Find out what scenarios we've ran into that are worth being mentioned and explained.
| Use case | Example |
|---|---|
| Network Monitoring | • Identify unknown or suspicious network traffic.
• Monitor bandwidth consumption and traffic levels. • Leverage IP and port filtering for baseline application behavior. • Export log data for reporting or live monitoring dashboards. |
| Usage Monitoring and Optimization | • Identify top talkers in the network.
• Leverage Geo-IP for cross-region traffic identification. • Utilize flow log data for capacity forecasting. • Identify and resolve unoptimized traffic rules. |
| Compliance | • Verify traffic rules adherence to network isolation and compliance obligations. |
| Network Forensics and Security Analysis | • Export flow log data to IDS or SIEM for analysis.
• Analyze network flow from suspicious IPs or network interfaces. |
How Azure NSG Flow Logs Work:
Azure NSG Flow Logs record IP flows in and out of an NSG, collecting data at one-minute intervals. This data, stored in JSON format, retains a default period of one year. While NSG Flow Logs are disabled by default, enabling and managing this service is achievable through Azure Portal, Azure CLI, and Azure PowerShell.
Enabling Azure NSG Flow Logs using the Azure Portal:
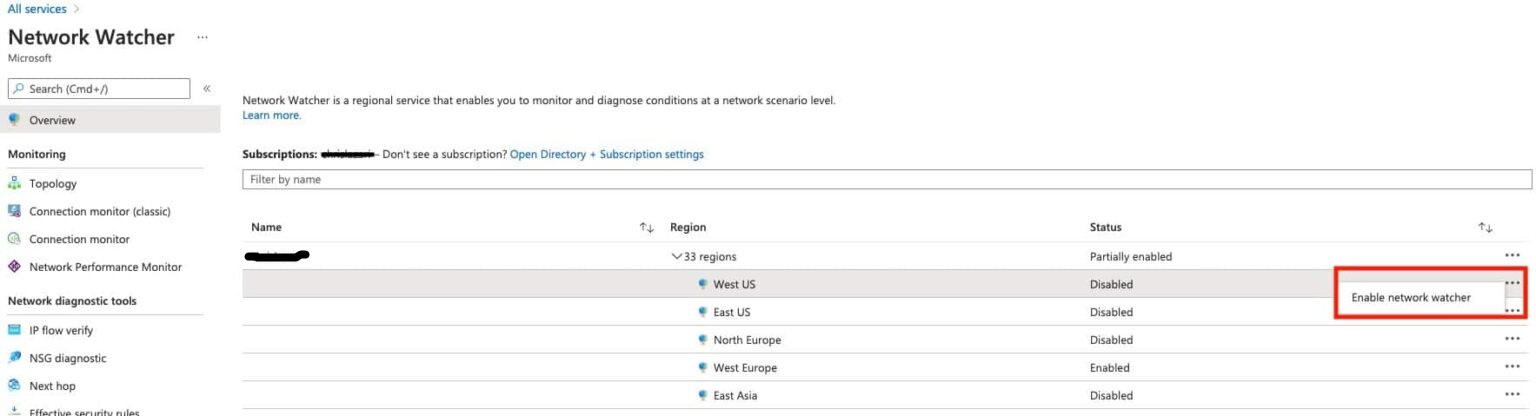
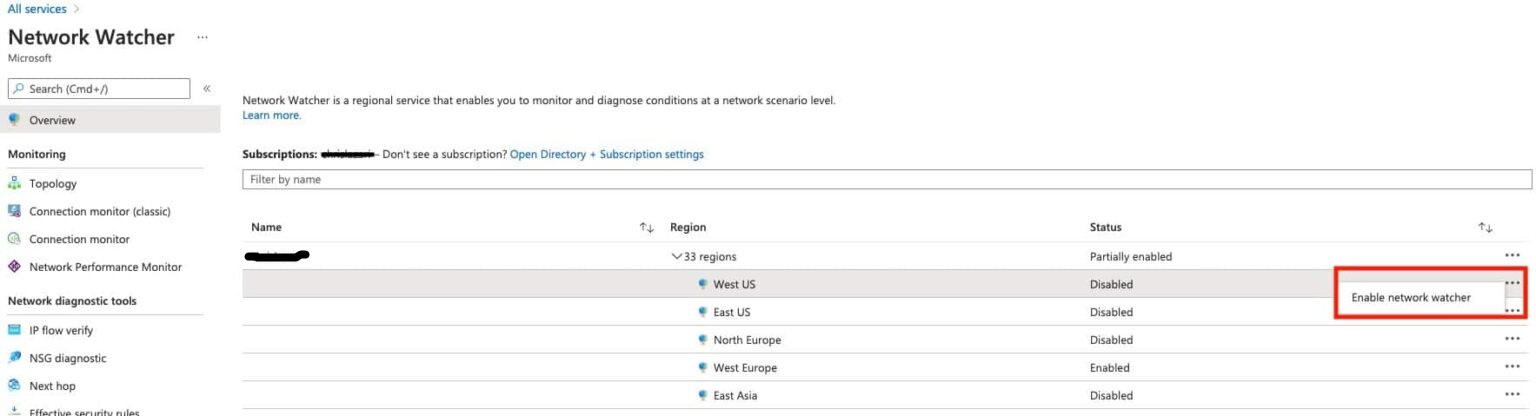
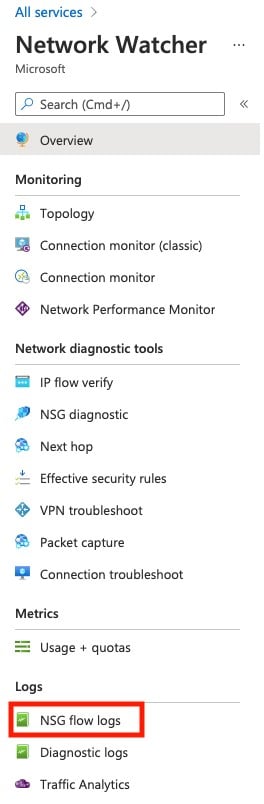
1. Enable Network Watcher: Search for Network Watcher, select the region, and enable it.
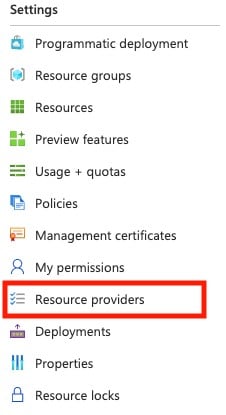
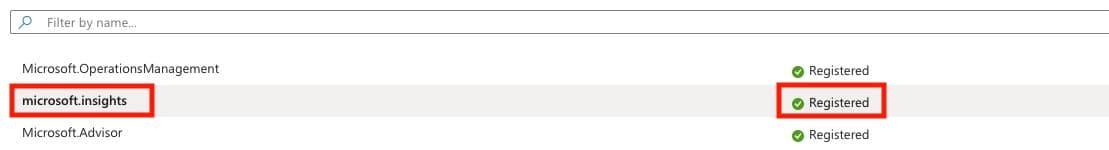
Note: The Microsoft Insights provider is a prerequisite for Azure NSG flow logging. You can search for Subscriptions, open the relevant subscription, and confirm microsoft.insights registration.
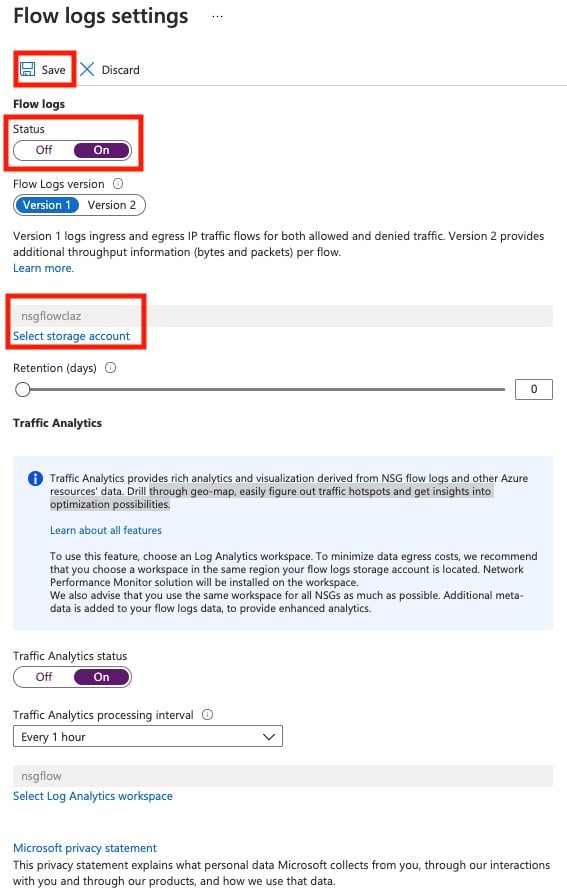
2. Enable NSG Flow Logs: Search for Network Watcher, select NSG flow logs, choose the NSG, set Flow log status to On, select storage account, and save.
Conclusion:
Azure NSG Flow Logs empower Azure users with detailed network visibility and analysis capabilities, contributing to robust security practices and efficient resource management.